安装
1 | https://github.com/paranoidninja/CarbonCopy.git |
usage
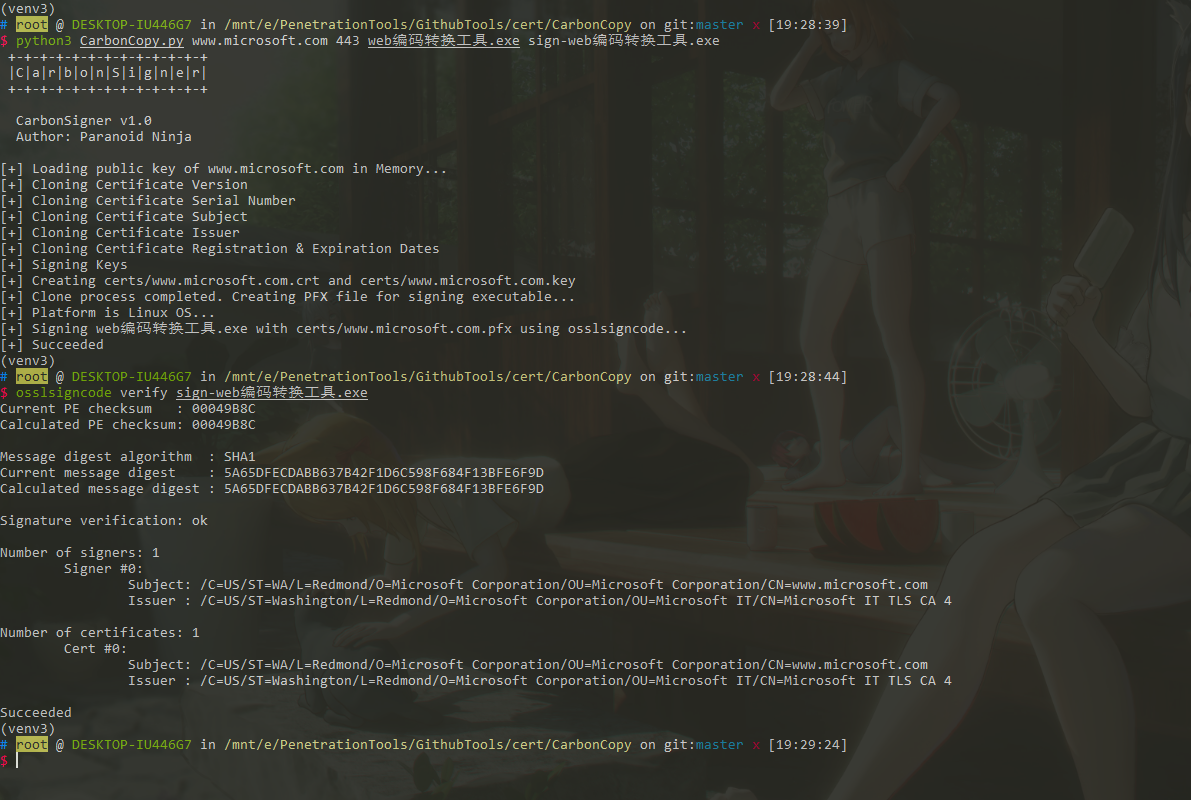
1 | python3 CarbonCopy.py www.microsoft.com 443 web编码转换工具.exe sign-web编码转换工具.exe |
代码中主要函数
获得host(www.microsoft.com)证书
1 | ogcert = ssl.get_server_certificate((host, int(port))) |
创建虚假的证书
1 | CNCRT = certDir / (host + ".crt") |
创建Keygen
1 | k = crypto.PKey() |
从原始证书加载设置证书详细信息
1 | print("[+] Cloning Certificate Version") |
加上证书
1 | shutil.copy(signee, signed) |
项目地址: